Ransomware like the ITRZ is unfortunately a real and growing threat. Cybercriminals constantly evolve their techniques to penetrate even the most secured systems, breaching our personal spaces. The purpose of this article is to help you understand the ITRZ ransomware, not just as a theoretical concept, but as a material threat to your digital safety.
Quick Links
Giving attention to the mechanism of this particular ransomware, we will lay bare its potential effect on your system. Furthermore, we will outline preventive measures to bolster your defense against such infections and provide a step-by-step guide to effectively remove the ITRZ ransomware, should your system be compromised.
What Is ITRZ Ransomware?
Substantial technological advancement has its fair share of pros and cons. One of the main drawbacks in the digitalization era is the persistent threat of cyber attacks, particularly in the form of ransomware. Among these digital perils, the ITRZ Ransomware has emerged as a significant concern for tech enthusiasts. Hence, it becomes vital to demystify how it infiltrates systems, giving security professionals and users alike the upper hand in mitigating its effects.

Ransomware is a type of malicious software crafted by cybercriminals designed to block access to a computer system until a sum of money, or “ransom,” is paid. ITRZ Ransomware is a strain of Djvu Ransomware family and exhibits the characteristic features of this form of cyber attack, encrypting personal files (alters file extensions to .itrz) and then demanding a ransom in cryptocurrencies for decryption.
How The Ransomware Attacks?
The mechanism of infiltration deployed by ITRZ Ransomware is as covert as it is effective. It typically exploits three major avenues to gain unauthorized access to systems, which are:
- Email Attachments and Spam Phishing Attacks: ITRZ Ransomware is often embedded in seemingly harmless email attachments. Unsuspecting users who open these contaminated attachments unsuspectingly instigate the malicious code’s execution.
- Malvertising and Compromised Websites: This involves exploiting insecure websites or advertisements. The user’s interaction with these compromised platforms results in unwanted software or code being downloaded, subsequently executing the ransomware.
- Software Vulnerabilities and Out-of-date Programs: Cybercriminals often exploit known vulnerabilities in outdated software. Regularly updating software is an essential step to prevent such unwanted invasions.
To remain proactive against the threat of ITRZ Ransomware, it’s crucial to become a part of the solution rather than the problem. This means employing a sturdy security protocol that addresses these areas of vulnerability. Practices such as refraining from opening unfamiliar email attachments, keeping software updated, and using robust security software that can detect and prevent ransomware attacks should be the way forward in this era dominated by the convenience of digital technology.
While the advent of ITRZ Ransomware might uncover an unprepared system’s vulnerabilities, comprehending its infiltration mechanics provides an opportunity to upgrade safety practices to thwart such cyber threats. By staying one step ahead, and remaining vigilant, the tech enthusiast doesn’t simply adopt technology but also ensures its safety from nefarious threats like ITRZ Ransomware.
Preventive measures
Building on this critical dialogue around ITRZ Ransomware, let’s delineate some specific, actionable measures that can further aid in fortifying your system against this devastating threat. While common sense measures like avoiding dubious emails and maintaining hardware and software primacy are imperative, there is an array of supplementary practices that could seal potential loopholes left out in these preliminaries.
1.) First and foremost, compartmentalizing your system is paramount. Enabling security features such as User Account Control (UAC) on Windows or Gatekeeper on MacOS can serve as a significant barrier preventing malware installation. Moreover, do not conduct everyday activity on an account with administrative privileges. Create a separate user account for daily work, hence preventing inadvertent authorizations of malicious activities on your system.


2.) Secondly, data backup should be a non-negotiable in every cyber hygiene routine. Despite your noblest efforts, an infiltration may sometimes be unavoidable. In such instances, uncompromised backup data can prove to be a lifesaver. Utilize automated local and cloud-based backup solutions to safeguard your data. Options like Windows’ in-built File History or MacOS’s Time Machine provide suitable local backup solutions, while services like Backblaze or Carbonite allow secure cloud backups.

3.) The third strategy revolves specifically around phishing emails, a common medium for ITRZ Ransomware infiltration. Training yourself to spot such emails can drastically reduce the chances of a successful breach. Be wary of generic greetings, poor grammar, and spelling mistakes, urgency, and requests for personal information. These are classic hallmarks of phishing attempts.
4.) Enabled macros have been identified as a significant Achilles’ heel in the fight against ransomware. Disable macros in your common applications to fortify your system against this type of breach, or, set macros to run in ‘disable all’ mode but consider exceptions if you trust the source.
5.) Lastly, consider a Software Restriction Policy (SRP) or a similar technology such as App Locker for Windows ecosystems. These tools limit the ‘allowed’ software, thus largely protecting your system from unauthorized executions.
Step-by-step removal process
Now we’re going to go deeper into techniques you can employ if your system is already infected with ITRZ Ransomware. Efficiently removing ransomware is a pillar in maintaining digital hygiene and it requires a dedicated, analytic and swift approach.
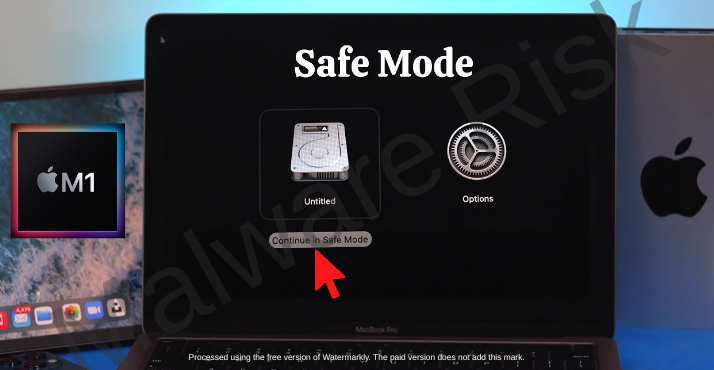
Step 1: Safe Mode Activation
Initiate the first step of ransomware removal by booting your system into ‘Safe Mode.’ For Windows users press the ‘F5’ or ‘F8’ keys when your PC is starting. For Mac users, press and hold the ‘Shift’ key after restarting your system. Safe Mode will restrict the ransomware’s activities while enabling your investigations.
Step 2: System Restore
After successfully booting into Safe Mode, consider restoring your system to an earlier, pre-infiltration state. Utilizing Windows ‘System Restore’ can effectively turn back time on the malicious intrusion, but only if you have restore points set from before the ransomware infection.

Step 3: Kill Malicious Processes
Post safe booting and system restoration, move on to identifying and killing the ITRZ Ransomware processes running on your system. Do this via the ‘Task Manager’ in Windows (press Ctrl + Alt + Del to access) or ‘Activity Monitor’ in MacOS. Look for resource-heavy processes that appear suspicious or unfamiliar, and terminate them.

Step 4: Ransomware Removal Tool
Now, download and install a specialist ransomware removal tool. Make sure to choose a top-tier, reputable provider, as the effective removal of ITRZ Ransomware heavily depends on the potency and efficiency of the tool. Options include Norton, Malwarebytes, Spyhunter, and Combo Cleaner but research adequately according to your system specifics.
Threat Removal With Malwarebytes Malwarebytes is a leading provider of antimalware software, dedicated to protecting users from the ever-growing threat of malware. With its advanced technology and comprehensive approach, Malwarebytes offers a robust solution to detect, prevent, and remove malicious software from computers and devices. Malwarebytes' antimalware software combines multiple layers of protection, including real-time scanning, behavior monitoring, and artificial intelligence, to identify and eliminate threats in real-time. This proactive approach ensures that users are protected from both known and emerging threats. It’s available as a free tool and we recommend it as a must have app on your device to keep your protected against threats. Step 1: Download Malwarebytes for your device by clicking on the link based on your operating system. Malwarebytes is available free of cost and can be used over cross platforms. However, the premium version offers more versatile features and protection to your device. You can register the app to premium version through in-app options or official website. Download Malwarebytes For Windows/Mac Step 2: Navigate to the folder where the installer file is downloaded and double click on it. The file is usually stored under “Downloads” directory.
Step 3: Once the installer runs, it opens Malwarebytes Setup Wizard with two options as Install and Advanced options. The Advanced option basically allows you to choose a directory where you want the app to install, select your language, and adding shortcuts. Just click on Install.
Step 4: You will now be asked to choose the type of protection you want, either Personal or Business. Based on your requirements, select the right option and click Next button.
Step 5: The setup will ask you to add a browser guard to keep your browsing safe. It’s an optional thing, but still you can choose adding the plugin to browsers to keep your online data safe. Once selected the appropriate option, proceed further to install the app. The installation process may end in a few minutes.
Step 6: After the installation is successfully done you can see a success notice. Click on Open Malwarebytes button now.
Step 7: After the Malwarebytes launches, click on the Scan button to start the scanner to identify present threats on your device.
Step 8: Sit back, wait and relax till the scanner searches for malicious traits on your computer. It may take time depending upon the storage size, and computer resources as well.
Step 9: After the scanning process completes, a screen with detected threats will appear before you. To remove detected malware or potentially unwanted programs from your device, click on Quarantine button.
Step 10: Malwarebytes may also ask you to restart your computer to complete threat removal process. So, just restart your computer. That’s it, your computer is now malware free. Threat Removal With Spyhunter SpyHunter is a powerful antimalware software designed to protect your computer from various threats, including malware, spyware, and adware. With its advanced scanning technology, SpyHunter can detect and remove harmful programs that may be lurking in your system. It also offers real-time protection to prevent new infections from occurring. SpyHunter is known for its user-friendly interface, making it easy for both novice and experienced users to navigate. It provides regular updates to ensure that your computer remains secure against the latest threats. If you're looking for a reliable antimalware solution, SpyHunter is definitely worth considering. Step 1: Download Spyhunter 5 for your device by clicking on the link based on your operating system. SpyHunter 5 Anti-Malware provides a 7-day fully functional Free Trial (15 days for Mac) with Credit card required, No charge will apply upfront. No charge if you cancel 2 business days before the trial ends. Download Spyhunter For Windows Download Spyhunter For Mac Step 2: Go to the directory where the installer is downloaded and stored. The file is usually stored under “Downloads” directory. Double click on the installer to run setup.
Step 3: Select your preferred language and click on OK button. This will initialize the installer, so click on the Continue button when prompted.
Step 4: You will be asked to accept the EULA and Privacy policy of the application to proceed the installation. So choose the option I accept the EULA and Privacy Policy, and click on Accept & Install Button.
Step 5: Now, the installation process will begin and progress bar can be seen. The process may take a while to complete, after which a successful installation notice is shown.
Step 6: The Spyhunter launches itself automatically following installation. Below mentioned screen will appear before you.
Step 7: Also, the scanner will start scanning your computer to identify present threats inside your device. During scan, it will show you detected threat’s name, security level, and details about the threat as well. Sit back & relax to complete the scan process
Step 8: The scanner once finished, click on Next button to proceed further.
Step 9: The app will ask you to buy its licensed version to complete the removal process. Alternatively, you can also avail a 7 day free trial under which the software will be fully functional to remove all threats.
Threat Removal With Combo Cleaner Combo Cleaner is a comprehensive security software designed to protect and optimize your Mac system. With its powerful features and user-friendly interface, Combo Cleaner offers a range of tools to keep your device safe from malware, adware, viruses, and other threats. It scans your computer thoroughly, detects and removes any malicious software it finds, and also cleans up junk files and unnecessary clutter to improve system performance. Combo Cleaner is known for its advanced algorithms and real-time protection, ensuring that your Mac remains secure and optimized at all times. Whether you are a casual user or a professional, Combo Cleaner provides a reliable solution to ensure the safety and efficiency of your Mac. Step 1: Click download button below to get Combo Cleaner for Windows/Mac on your device. Combo Cleaner Antivirus is available to download as free scanner. The scanner will scan and detect all inside threats on device, but users need to buy its license key to avail complete removal of threats. Download ComboCleaner For Windows Download ComboCleaner For Mac Step 2: Browse to the directory where the installer is downloaded (usually in ‘Downloads’ folder), and double click on the installer to start installation.
Step 3: The installer begins and will ask you to set some necessary parameters like creating shortcuts, starting the app on windows startup and more. Choose the right options based on your needs, and click Next button.
Step 4: The installer now starts to install Combo Cleaner on your device and will complete it in just a few minutes.
Step 5: Once the installation completes, click on Finish button. Do make sure the option “Launch Combo Cleaner and run initial computer scan” is checked.
Step 6: The initial computer scan will start with updating and installing Combo Cleaner antimalware database updates. It will take some time depending upon your internet speed, and other resources.
Step 7: After the database updates are successfully installed, the antimalware solution will start scanning your device for present malware threats. Sit back and relax to let the app complete its process.
Step 8: After the scanning completes, a screen appears with all detected threats on your device. Just click on Remove All Threats button. Threat Removal With Norton Antivirus Norton 360 is a comprehensive antivirus software that offers robust protection against various online threats. With its advanced features and real-time scanning capabilities, it ensures the safety of your devices and personal information. This antivirus software not only detects and removes viruses, malware, and spyware but also provides a firewall to protect your network from unauthorized access. Norton 360 is compatible with multiple platforms, including Windows, Mac, and mobile devices, providing a seamless experience across all your devices. Its user-friendly interface allows you to easily navigate through its various features and customize your security settings according to your preferences. Stay protected with Norton 360 and enjoy a worry-free online experience. Step 1: Click on the button below to get Norton 360 protection for your device. Norton 360 Antivirus is available and accessible over cross platforms. It provides a 7 day fully functional free trial with Credit Card. No charge deduction till trial period. Download Norton 360 For Windows/Mac Step 2: Download the installer and run it on your device. Click on Install button to proceed with installation steps further.
Step 3: The installation process will begin now with an increasing progress bar. Wait for the installation to complete.
Step 4: After the installation process completes, launch Norton 360 and click on Quick Scan option to start scanning device for threats.
Step 5: The scanner will initialize scanning computer for threats. This process may take some time depending upon the disk size and hardware resources of device.
Step 6: Once the scanner finishes, it will take all appropriate action against detected threats automatically. Click on Finish button to close the app.
Step 7: If you have purchased Norton’s license key, we suggest you to activate the application by clicking on Activate Now option.
Step 8: Norton 360 will now connect with its server to complete activation.
Step 9: Congratulations, your device is now protected with Norton 360 against all threats. |
Step 5: File Recovery Tools
Post malicious process termination and ransomware deletion, consider a file recovery tool to retrieve your lost or encrypted data. While not always successful, tools like ‘Shadow Explorer’ or ‘Recuva’ may help restore files from system ‘shadow copies’ or recover deleted files. Remember, this depends on the ransomware variant and its impact on your system.
Step 6: Password Change
Lastly, after the ITRZ Ransomware has been removed, make sure to change all your passwords, including system, social media, email and banking. This is particularly pertinent as many ransomware variants also install keystroke loggers or other spying mechanisms to steal login credentials.

Remember, dealing with ITRZ Ransomware requires technical savvy, precision and a dash of tenacity. However, if the steps seem too complex, seeking professional help is a wise move. Post removal, ensure a robust digital defense strategy to shield your systems from such ransomware attacks in the future. Stay tech smart, stay safe!
Wrapping Up
Through understanding the dangers and intricacies of ITRZ ransomware, we empower ourselves to guard our digital domains effectively. Protecting ourselves is not just about timely software updates and secure personal online habits, but it also lies in our thinking pattern, of being cautious and proactive in identifying potential risks. While the ITRZ ransomware removal process can be taxing, with a patient approach, it is indeed manageable. Ultimately, being informed and prepared makes us not just users, but responsible custodians of our digital space in this ever-evolving cyber landscape.

Nishant Verma is a senior web developer who love to share his knowledge about Linux, SysAdmin, and more other web handlers. Currently, he loves to write as content contributor for ServoNode and also collaborated with MRLabs now.






























